VMware’s Price Revolution: How Broadcom’s Changes Are Reshaping Mid-Market IT Strategy
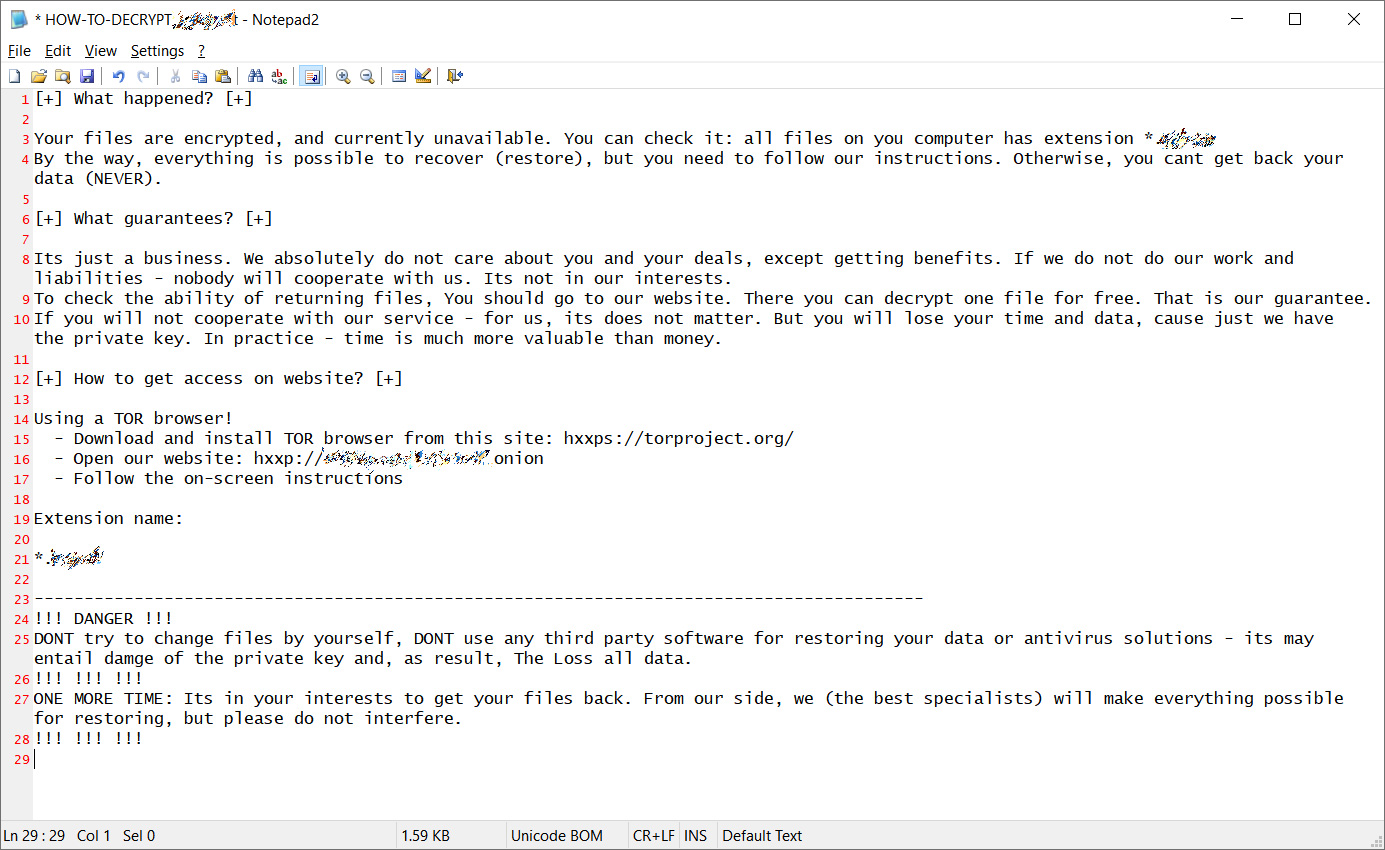
Feeling Renewal Pain
Bottom Line: Broadcom’s acquisition of VMware has triggered dramatic price increases of 800-1,500% for many customers, forcing mid-market organizations to urgently evaluate alternatives like Microsoft Hyper-V to maintain cost-effective virtualization infrastructure.
Since Broadcom acquired VMware in November 2023, the virtualization landscape has undergone seismic shifts that are particularly devastating for small and medium-sized enterprises (SMEs). What began as a strategic acquisition has evolved into a pricing revolution that’s forcing thousands of mid-market organizations to fundamentally reconsider their IT infrastructure strategies.
The Scale of the Price Shock
The numbers are staggering. Some customers report price increases ranging from 800% to 1,500%, while some organizations face even more dramatic hikes. AT&T claimed Broadcom offered them a 1,050% price increase, transforming their annual VMware costs from manageable to prohibitive overnight. For context, these aren’t modest adjustments—they represent a complete overhaul of the economic equation that made VMware attractive to mid-market clients.
The pricing transformation isn’t just about higher numbers. Broadcom has fundamentally restructured how VMware products are sold and licensed. The company eliminated approximately 8,000 individual product SKUs, consolidating them into just two primary bundled offerings: VMware Cloud Foundation (VCF) and vSphere Foundation. This consolidation forces customers to purchase entire suites rather than selecting specific components they actually need.
The Mid-Market Squeeze
Mid-market organizations are caught in a particularly painful position. Unlike enterprise customers who might already use multiple VMware products and could potentially benefit from bundling, smaller companies typically relied on standalone solutions like vSphere Essentials Plus—which Broadcom has now discontinued. These organizations suddenly find themselves forced into enterprise-grade bundles that include features like NSX networking and vSAN storage they never requested or needed.
The new core minimums compound the problem. Starting April 2025, VMware enforces a minimum 72-core license subscription for products like vSphere Standard, up from the previous 16-core minimum. For organizations running smaller deployments or edge locations, this means paying for licenses that far exceed their actual needs. It’s like being forced to buy a truck when you only need a bicycle.
The transition from perpetual licenses to subscription-only models adds another layer of financial pressure. Many mid-market companies relied on the predictable, one-time costs of perpetual licenses that could be amortized over several years. The new subscription model transforms capital expenditures into ongoing operational costs, fundamentally altering budget planning and cash flow management.
We’ve actually run into instances where Broadcom is quoting OVER published list price for clients that they feel they can extort with a higher cost.
The Search for Alternatives
Faced with these dramatic changes, mid-market organizations are actively exploring alternatives, with Microsoft Hyper-V emerging as the most compelling option for many. The appeal is both strategic and economic.
Cost Advantages: Hyper-V is included with Windows Server licenses at no additional cost, providing immediate relief from VMware’s pricing pressure. For organizations already invested in Microsoft’s ecosystem, this represents enormous potential savings. While enterprises might need additional management tools like System Center Virtual Machine Manager, the base virtualization capabilities come without separate licensing fees.
Technical Maturity: Modern Hyper-V has evolved far beyond its early limitations. Windows Server 2025 includes significant enhancements to GPU partitioning for AI workloads and improved scalability that now supports up to 24TB of host memory—actually surpassing VMware in some specifications. Features like Live Migration, high availability clustering, and robust security through Shielded VMs provide enterprise-grade capabilities that match much of what VMware offers.
Integration Benefits: For organizations running Windows-centric environments, Hyper-V offers seamless integration with Active Directory, Group Policy, and Azure cloud services. This tight integration often translates to simplified management and reduced administrative overhead compared to managing separate VMware infrastructure alongside Microsoft systems.
Migration Feasibility: While migrating from VMware to any alternative requires careful planning, Hyper-V’s similarities in core virtualization concepts make the transition more approachable than some alternatives. Many organizations are discovering that their Windows-based workloads migrate relatively smoothly to Hyper-V environments.
Strategic Considerations for Mid-Market Leaders
The decision to migrate away from VMware shouldn’t be taken lightly, but the current pricing environment makes exploration essential. Organizations should conduct thorough assessments of their current VMware usage, identifying which features are truly necessary versus those that could be replaced with alternative solutions or eliminated entirely.
The migration window is critical. Existing VMware customers still operating under older support agreements have time to plan, but that window is closing. Organizations should begin testing alternatives immediately, even if they ultimately decide to remain with VMware under new terms.
For many mid-market companies, this crisis presents an unexpected opportunity to modernize their infrastructure approach. Some are discovering that moving workloads to public cloud platforms or adopting hybrid strategies provides better economics than either VMware or on-premises alternatives.
Looking Forward
Broadcom’s transformation of VMware reflects a deliberate strategy to focus on larger, more profitable customers while shedding smaller accounts. For mid-market organizations, this reality demands urgent action. The days of affordable, flexible VMware solutions for smaller deployments appear to be ending permanently.
The good news is that alternatives like Hyper-V have matured significantly and can now handle most workloads that previously required VMware. Combined with cloud-native solutions and modern infrastructure approaches, mid-market organizations have viable paths forward—but only if they act decisively.
The virtualization landscape is experiencing its most significant disruption in decades. Organizations that move quickly to evaluate and implement alternatives will be best positioned to maintain cost-effective, capable infrastructure. Those who delay risk being trapped in unsustainable licensing agreements that could constrain their growth and innovation for years to come.
The revolution is here. The question isn’t whether change is coming—it’s whether your organization will lead or follow in responding to it.