Ransomware and the impact to your business
Everyday, you read another story about how a company has been hit by a ransomware attack, which potentially can disrupt your business, services to your clients and livelihood of your employees.
Just last week it was announced another company, Forward Air, was hit by a ransomware attack, which disrupted services and impacted revenue. This attack was attributed to a group “Hades”. Forward Air, a trucking company from Tennessee, posted revenues of $1.4 billion in 2019 and employs more than 4300.
The ransomware note, resembles a similar note used by another ransomware group known as “REvil”, also known as “Sodin”.
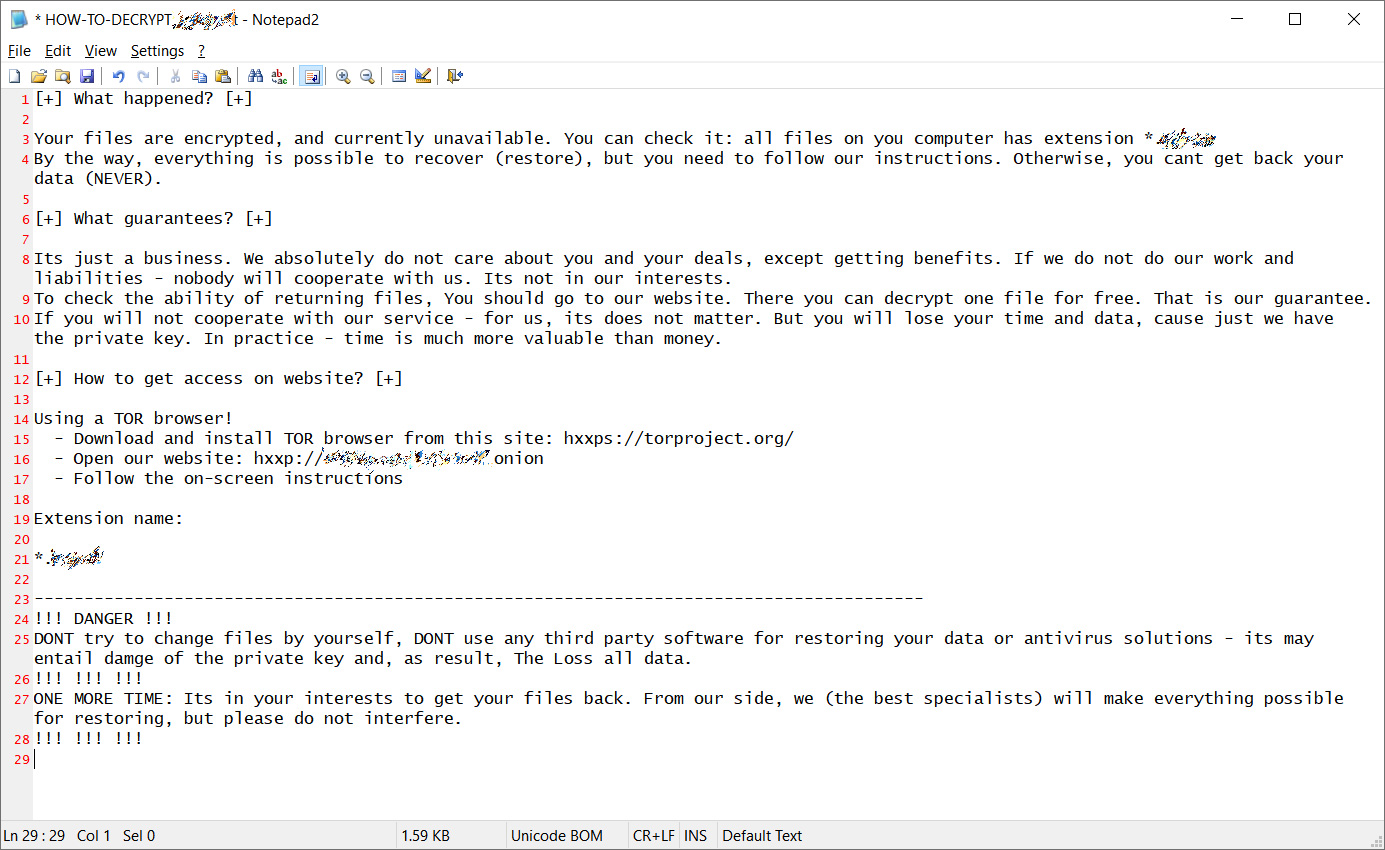
This is a Sodinokibi variant that was first seen in early 2019. Sodinokibi is what is known as ransomware-as-a-service, basically a software package which is catered by underground vendors to threat actors providing them a ransomware platform tool.
Companies are limited in their ability to defend against this type of exploitation, especially if they do not have full time IT staff or contracted Managed Service Providers that focus on security. Your organization must follow the following guidelines to help mitigate your exposure:
- Patch aggressively so vulnerabilities are eliminated and access routes are contained
- Enable endpoints with tools that automatically detect and respond to infections before they become systemwide
- Enable network threat intelligence tools to detect anomalies in your network traffic
- Make sure emails are screened for malicious payloads and links
- Minimize access levels by employees to perform their job functions
If you have been hit by ransomware, or just want to assess your company’s state of preparedness, reach out to us to discuss your needs.
LMJ is a full service Managed Service Provider, with offices in Alaska and California.




