So you have secured your business.
Firewall, VPN for work from home, radius authenticated WiFi or perhaps an RDS gateway for remote desktops. Anti-virus is up to date, patching is top notch, SaaS applications locked up with two-factor authentication.
What about educating your workforce? Although Phishing is only the 5th most common primary cause of security incidents (per the Verizon 2020 Data Breach Report), following Denial-of-Service (DoS), data loss, Command and Control, or misdelivery of email/data – when it comes to data breaches Phishing is still number one.
Without a solid training plan for your employees, your business is at greater risk to have data compromised.
Top areas to look out for:
- Social Engineering
- Stolen Credentials
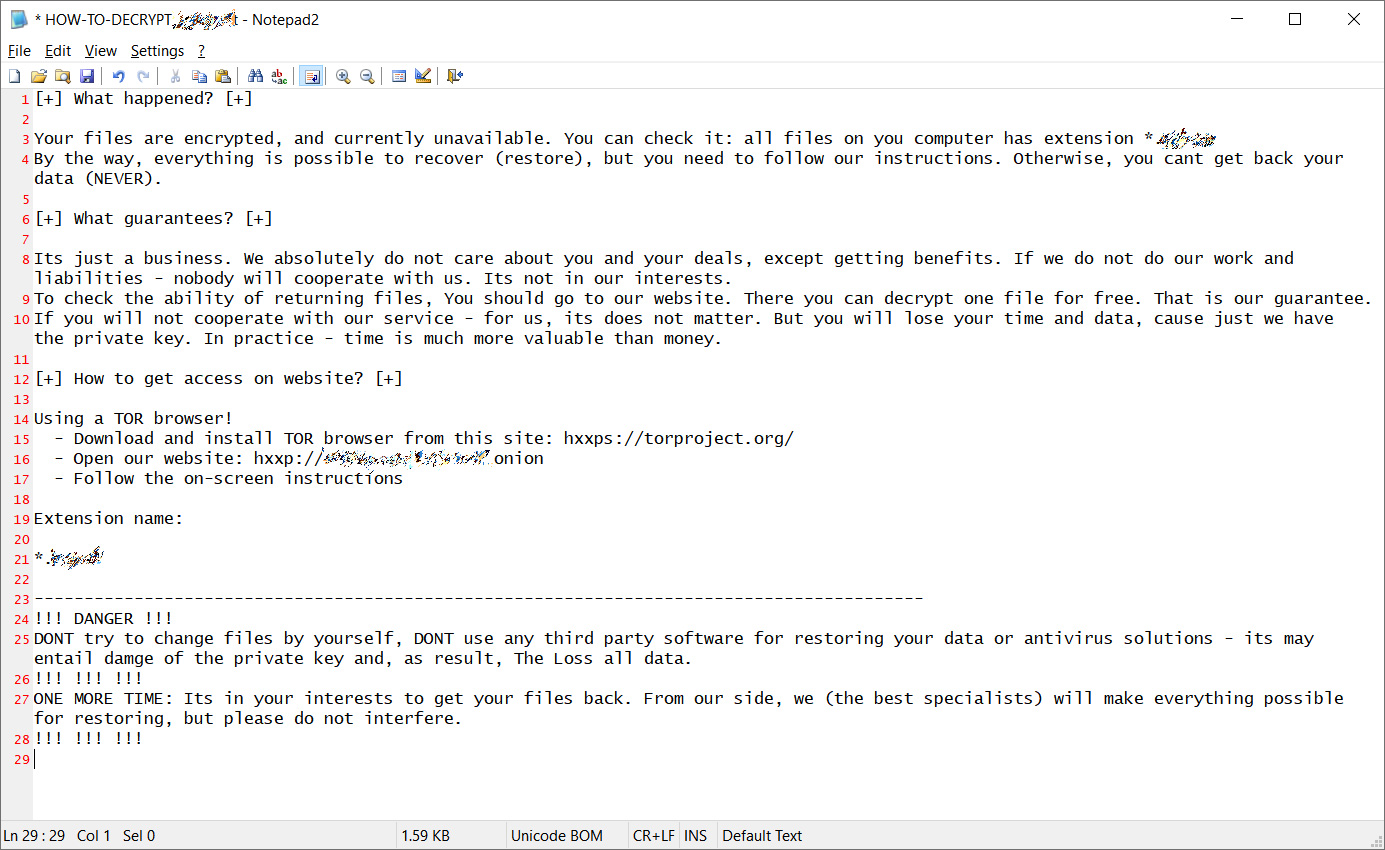
- Malware (usually delivered via email)
According to Verizon, Phishing is the first step in about 20% of security incidents and plays a role in another 30% of secondary steps to gain access to your information.
Highlights by Sector
Financial and Insurance:
- 1,509 incidents, 448 with confirmed data disclosure
- What did they target, Web Applications, Miscellaneous Errors and Everything Else
represent 81% of breaches
- External to company (64%), Internal (35%), Partner (2%), Multiple (1%) (breaches)
- Financial motive (91%), Espionage (3%), Grudge (3%) (breaches)
- What did they get- Personal data (77%), Other (35%), Credentials (35%), Bank (32%)
(breaches)
- How do they solve the problem -Implement a Security Awareness and Training Program (CSC 17),
Boundary Defense (CSC 12), Secure Configurations (CSC 5, CSC 11)

Healthcare:
- 798 incidents, 521 with confirmed data disclosure
- Miscellaneous Errors, Web Applications and Everything Else
represent 72% of breaches.
- External (51%), Internal (48%), Partner (2%), Multiple (1%) (breaches)
- Financial motive (88%), Fun (4%), Convenience (3%) (breaches)
- What did they get – Personal data (77%), Medical (67%), Other (18%), Credentials (18%)
(breaches)
- How do they solve the problem – Implement a Security Awareness and Training Program (CSC 17),
Boundary Defense (CSC 12), Data Protection (CSC 13)
But my company is too small for someone to try and get our data!
While differences between small and medium-sized businesses (SMBs) and large organizations remain, the movement toward the cloud and its myriad web-based tools, along with the continued rise of social attacks, has narrowed the dividing line between the two.
As SMBs have adjusted their business models, the criminals have
adapted their actions to keep in step and select the quickest and easiest path to their victims.
Contact us to get more information on our security practice and how you can have your team trained on cyber-security awareness.